In an era of digital surveillance, network throttling, and region-based restrictions, internet users are increasingly searching for tools that go beyond mainstream virtual private networks. While popular VPN brands dominate advertising space, tech-savvy communities often recommend lesser-known solutions that offer innovative approaches to privacy and censorship resistance. These hidden tools are not always beginner-oriented, but they provide powerful features for users who prioritize anonymity, decentralization, and control.
TLDR: Privacy-conscious users are turning to lesser-known VPN tools that provide advanced censorship resistance and stronger anonymity. These six hidden tools emphasize decentralization, traffic obfuscation, and Tor integration. While some require technical knowledge, they offer powerful alternatives to mainstream VPN services. For users in restrictive environments, these tools can significantly enhance digital freedom.
Below are six user-recommended VPN and VPN-like tools that operate under the radar yet deliver remarkable privacy benefits.
1. Mullvad with Advanced Obfuscation
Mullvad may not be quite as hidden as it once was, but among privacy circles it remains a favorite for features that casual users often overlook. Unlike many competitors, Mullvad does not require an email address to create an account. Users receive a random account number, minimizing personally identifiable information.
What makes Mullvad stand out in censorship-resistant contexts is its support for:
- WireGuard and OpenVPN with customizable ports
- Bridge mode for bypassing deep packet inspection
- Multihop connections
- Integration with the Tor network
In restrictive countries, advanced obfuscation settings can help disguise VPN traffic as regular HTTPS traffic, making detection more difficult.
Users appreciate Mullvad’s transparent pricing and infrastructure transparency reports. For privacy purists, its no-nonsense approach and minimal data retention policies make it a strong contender.
2. IVPN with Anti-Tracking Firewall
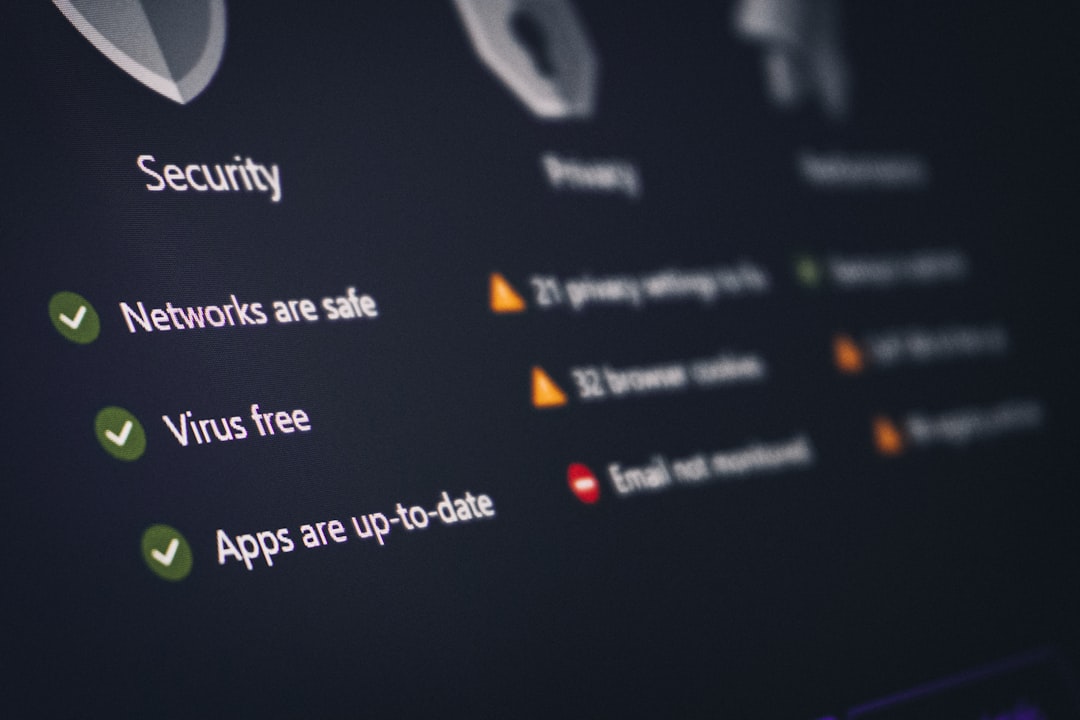
IVPN is frequently praised in privacy forums for its transparency and powerful anti-tracking tools. While it operates like a traditional VPN, its built-in firewall and customizable kill-switch features make it particularly useful in hostile network environments.
Key features include:
- Anti-tracker blocking malware and ads
- Multi-hop routing
- WireGuard support with rotating keys
- Open-source applications
The rotating key mechanism is especially noteworthy. By frequently changing cryptographic keys, IVPN reduces the risk of long-term traffic correlation attacks. This can be useful for journalists, activists, and individuals dealing with sensitive communications.
Although IVPN is not designed specifically as an anti-censorship tool, its stealth configurations help users bypass moderate filtering and throttling.
3. Outline by Jigsaw
Outline is an open-source tool developed by Jigsaw, a technology incubator created by Google. It takes a slightly different approach compared to commercial VPN services. Instead of subscribing to a shared infrastructure, users create and manage their own VPN server.
This self-hosted model offers several advantages:
- Reduced likelihood of IP blacklisting
- Greater control over server location
- Customizable access sharing
Because users deploy their own servers through cloud providers, Outline connections can blend in with ordinary cloud traffic. In highly censored environments, this makes detection significantly harder.
However, Outline requires some technical knowledge. Users must manage server costs and basic deployment steps. For those comfortable with cloud platforms, it is a powerful censorship-resistance tool.
4. Lantern
Lantern operates more like a peer-to-peer circumvention tool than a conventional VPN. It routes traffic through a distributed network of volunteer and cloud-hosted servers.
Its intelligent traffic routing system automatically determines the fastest and least restricted path. This makes Lantern particularly useful in countries where websites are selectively blocked.
Why users recommend Lantern:
- Automatic traffic obfuscation
- Peer-assisted routing
- Ease of use for non-technical users
Lantern does not offer the same level of anonymity as Tor or advanced VPN setups. However, its convenience and adaptive routing make it valuable for individuals simply trying to access restricted websites quickly and reliably.
5. Psiphon
Psiphon has long been a trusted circumvention tool in heavily censored regions. It combines VPN, SSH, and HTTP proxy technologies into a single platform that automatically selects the best protocol based on network conditions.
This hybrid design increases resilience against blocking measures. If one protocol is detected and blocked, Psiphon can switch to another.
Core advantages include:
- Dynamic protocol switching
- Wide availability on mobile platforms
- Strong anti-censorship focus
While Psiphon may not match premium VPN services in raw speed, its adaptability makes it highly valued in regions facing aggressive internet filtering.

6. Tor with VPN Layering
Though Tor itself is not a VPN, many advanced users combine it with VPN services for enhanced privacy. This setup—sometimes called VPN-over-Tor or Tor-over-VPN—adds an extra layer of abstraction between users and their online activity.
There are two common configurations:
- VPN → Tor: Connect to a VPN first, then access the Tor network.
- Tor → VPN: Enter the Tor network before connecting to a VPN.
The first method is generally easier and protects the user’s real IP address from Tor entry nodes. The second method can conceal Tor usage from the ISP, though it requires advanced configuration.
This layered approach is not necessary for everyday browsing. However, for individuals dealing with surveillance-heavy environments, it provides:
- Enhanced anonymity
- Resistance to traffic correlation
- Stronger protection against monitoring
Users should note that combining Tor with a VPN can reduce connection speeds significantly. Proper setup and understanding of threat models are essential.
Choosing the Right Tool
Each of these hidden VPN tools serves a slightly different purpose. Some prioritize anonymity, others focus on bypassing censorship, while a few emphasize decentralization and user control.
Factors to consider when selecting a solution include:
- Your technical skill level
- The severity of censorship in your location
- Your need for anonymity versus simple website access
- Speed and usability requirements
For example, a journalist in a restrictive regime may favor Tor combined with a privacy-focused VPN. A casual user trying to access region-locked streaming services might find Lantern or Psiphon sufficient.
Ultimately, privacy is not one-size-fits-all. The most effective strategy often involves understanding potential threats and selecting tools accordingly.
Final Thoughts
Mainstream VPN services may dominate advertising, but privacy communities consistently discover innovative alternatives that provide enhanced control and censorship resistance. From self-hosted servers like Outline to hybrid circumvention platforms like Psiphon, these tools demonstrate that digital freedom is still achievable with the right knowledge.
As surveillance technologies evolve, so too must privacy strategies. Staying informed about lesser-known solutions ensures users can adapt and maintain open access to the global internet—even in restrictive environments.
FAQ
1. Are hidden VPN tools safer than mainstream VPNs?
Not necessarily safer, but they often offer specialized features such as obfuscation, self-hosting, or Tor integration. Safety depends on proper configuration and user awareness.
2. Can these tools completely prevent government surveillance?
No tool can guarantee complete protection. However, combining strong encryption, obfuscation, and anonymity networks can significantly reduce exposure.
3. Is Tor better than a VPN?
Tor offers stronger anonymity through multi-layer routing, but it is slower. A VPN provides faster speeds and easier usability. The best choice depends on your threat model.
4. Do these tools work on mobile devices?
Many do. Psiphon and Lantern have strong mobile support, while Mullvad and IVPN provide mobile apps. Self-hosted tools like Outline can also be configured for smartphones.
5. Are free options reliable?
Some free tools like Psiphon and Lantern are legitimate, especially for censorship resistance. However, users should research carefully and avoid unknown services with unclear privacy policies.
6. Is technical knowledge required?
It depends on the tool. Lantern and Psiphon are beginner-friendly, while Outline and Tor layering require more advanced understanding.